I’ve had more than half a dozen friends and colleagues ask for my help in restoring encrypted files after a ransomware attack in as many months. Unfortunately, when ransomware is done “right” there’s little you can do other than restore from a backup and start again. You do have good backups, don’t you?
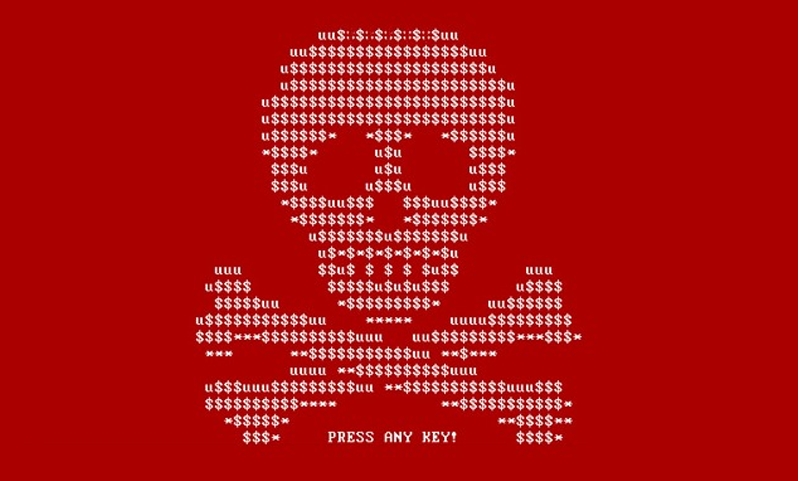
Ransomware (like Cryptowall, Wannacry or Petya) is a type of malware that works by encrypting each personal document it finds and then deleting the original. It sends the key to its home servers and destroys the original local copy of the key. This leaves the victim with a bootable computer and a hard drive full of inaccessible files. A “ransom note” is left on the computer requesting bitcoin to be sent to an anonymous address. As nefarious as this seems, the customer service department of ransomware operations is quite good - I’ve talked to many people who paid the ransom and then were able to restore their file. The ransomware business model, ironically, supports better customer service than your local cable or internet provider.
Ransomware seems to be everywhere in the news right now. The cities of Baltimore, Newark, Atlanta, Sarasota, and the UK’s NHS have all suffered major outages from ransomware attacks. After the city of Baltimore was infected, one friend told me he wasn’t able to pay his water bill for more than a three months. Luckily, for him, the city also wasn’t able to shut his water off for failure to pay. Ransomware could be an issue in the upcoming election, too.
Ransomware is not new, the first ransomware was discovered in 1989, called PC Cyborg. It required users to send $189 to a post office in Panama. Luckily for most people infected there was a major flaw in the algorithm which made it easy to reverse the damage done.
Sometimes you get lucky and the ransomware authors will make mistakes. It’s worth searching for, and trying, different ransomware decryption tools. Most people in the security industry are unified against ransomware, therefore most decryption tools are free. Take a look at the Avast and Kaspersky decryptor lists if you get hit. Unfortunately, many types of ransomware follow encryption best practices since their revenue depends on it. They choose good algorithms, generate random keys, and don’t roll their own crypto.
What’s the best defense? Keeping your software up to date, running software like Crowdstrike Falcon or other anti-malware, and taking care with attachments and browsing behavior can all help, but there is no better protection than having a backup and restore strategy that will allow you to recover when disaster strikes.